To protect oneself in this generation means protecting your personal data as well. It is a necessity for anyone to keep their details secured on any website they visit because many vicious cybercriminals are around to cause harm.
Even in ancient times, keeping your precious valuables is of high priority, which they do in various different ways. Some keep their treasures six feet deep into the ground, some keep it in a vault, while others just keep it somewhere secret and unknown to anybody else because they believe it is only for their own use.
Nowadays, such manners of storing and hiding can no longer work, especially with the presence of technology. People think they could not live without the internet. In fact, some would be sharing each moment of their life through a photo or video that they would share with everyone online in a post on social media.
Because everybody seems to be so engrossed with the use of technology, more scammers are becoming enticed to do some unlawful acts through this platform. People become at risk without them knowing it because they are having a great time browsing and surfing the internet.
Some of the various crimes and threats that exist today through the use of the internet include phishing scams, malware, different forms of theft, hacking and spamming, e-money laundering, investment fraud, cyberstalking, identity theft, ransomware, and many more other serious violations.

- Phishing scams are conducted to lure and deceive people into sharing sensitive details about their bank accounts, transactions, as well as credit card information. They are people not familiar to you but will suddenly just message you one day, asking for such vital data. Scammers are good at convincing and attracting users to the point that they shall willingly give in to what they are asked for.
- Malwares are a variety of types, such as the notorious ‘spyware’ and ‘trojan.’ This type of software is made with the intention of causing harm to a person’s details as well as the device itself. It works by sending out a series of destructive viruses before it totally damages your system and eventually steals whatever it pleases. Through this software, scammers can get some valued personal details which they will use to track your bank accounts or your credit card details. Checking your bank activity regularly then becomes a responsibility you should never forget to fulfill.
- Theft that comes in various forms like identity theft are serious ones because of the strong impact it leaves on someone’s life. To steal somebody else’s ID is a big crime, especially if you will be using it to manipulate accounts, steal money, and deceive people.
- Hacking and spamming, which is mostly aimed at targeting social media accounts where most users tend to be careless in the things they post online. It is because users think it is just fine to share whatever they like. That is why hackers get an easy way out to do their thing. Hacking, by the way, is the act of breaking into another person’s personal account on social media such as Twitter, Facebook, and Instagram. Once able to open the account, some hackers just make fun of the owner’s identity and reputation by posting ridiculous things using such an account, while others use the information they gathered from the account to make fake announcements and transactions, too.
Whereas, spammers are those who send out malicious emails and contents that users did not directly request. The catch for them is that, once they download or even simply click a link or attachment on that email, their device gets infected as well as their account. In one click, everything can change, so proper care before clicking is highly necessary.
- E-money laundering is a crime committed through online bank transfers that are so easy for scammers to manipulate due to banks’ not accepting this fault as their responsibility. This often occurs, too, due to the huge number of transactions made each day that banks are no longer able to monitor them closely one by one.
- Investment fraud is the use of contact details and account information that are originally meant for savings, investment accounts, etc. However, with fraudsters themselves being knowledgeable about sales and investment matters, creating a fraud as an investment broker, for example, is simple. You’ll never suspect of their intention because they know exactly what they are talking about and what they are aiming for.
- Cyberstalking is most common among teenagers, lovers, and fans who are after the activities of someone they like so they will get to know about them more. That’s on the good side of it. On the other hand, the negative side of that is some scammers do this cyberstalking to cause someone harassment and distress since they’ve known a lot of things about the other person.
- Identity Theft is a serious violation also which entails the use of details about another person for scamming purposes. This is most commonly conducted to gain money from people who are not aware that their ID is being used by a scammer. It includes credit card information and addresses, too.
- Ransomware, as its name suggests, is a type of malware that asks for a ‘ransom’ before an account owner can reopen his or her files that this threat has encrypted. This malware enters a computer, goes through its files, and then encrypts all of them, which prohibits users from opening nor viewing their own documents. After a while, a notification demanding an amount of money as a fee for the scammers to decrypt their files is sent to users. It causes anxiety and distress among most users, especially young adults who encounter this. That’s exactly why ransomware is the most notorious of all today.
All of the abovementioned threats sound serious and needs immediate action to prevent your computer and your identity from being affected by it. Thus, some programs and software are designed recently to fight this problems all away. Learn about them further on the list below.
- Microsoft Bitlocker – everything on your drive is kept clean, and your documents always safe, too. The passwords you use are also safer than with other encryption software.
- Tor – free to download by anyone looking for security and safety. This second-gen routing system is made to enable users to make communications on the internet anonymously.
- Endpoint Encryption – this one is applicable for more types of devices such as computers, desktops, Mac, and USB drives as well. Full disk and folders are ensured with 100% safety.
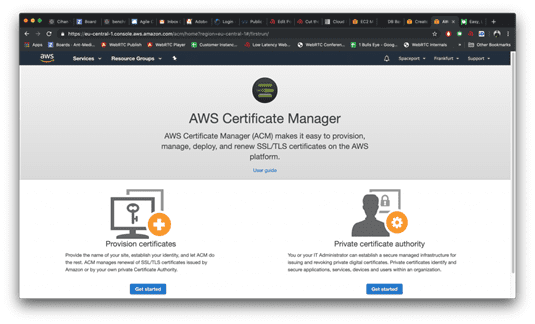
- AWS Certificate Manager – lets users get easy to provision and management of certificates that are used to provide a protected network from outside elements.
5. Boxcryptor – dedicated for the use of Dropbox & Co. for end to end or one-way communication between the permitted parties.
6. Sophos Safeguard Encryption – allows a kind of protection that covers all forms of data in various platforms that will not cause logs or slow in connection.
7. VeraCrypt – applicable for Mac OSX, Windows, and Linux is free downloadable encryption software that offers total safety.
8. TokenEx – is a platform for several kinds of data channels that offer unstoppable Flexi customer’s use and storage.
9. Keybase – newest security and safety app that is allowed on mobile phones, desktops, and computers. This is for everybody’s use, but not as secure as the rest on the list.
10. Box KeySafe – full control is given to any user of this encryption software, which makes no impact on your experience while using the internet.

Final Thoughts
Some things are meant to be shared while others are meant to be kept for yourself alone. It may be through whichever way you want, but what matters is you are sure of your security and safety online. You and only should be making use of your identity and nobody else. Otherwise, they’ll have to pay for it and take charge of the consequences it will cause them afterward, too.