Consult an expert in information and communication technology (ICT), and he or she would probably agree: encrypted communications were among the most efficient ways to secure data from internet activities. It does not entirely protect the access of data by cybercriminals or malicious people. Instead, encrypted to prevent these legitimate access from observing the data and thus using it.
As a consequence, tedious hardware encryption will help smaller businesses strengthen their data privacy. Processing refers to encryption and authentication using programs. When running a cryptography program, the previously recognizable data will be translated into indecipherable code comprising of upper case, small letters, alphanumeric characters.
Other information you need to consider about disk encryption software
Complete multifactor authentication, as the title indicates, is an IT method requiring encrypted communications of all the information from a single disk drive. All information collected on the corresponding journey will be authenticated, from massive office programs to network-attached documents and passwords. The first and only component that is not validated is the boot sector history (MBR) with complete hardware encryption. Full hardware encryption is an easy and secure way of shielding your encrypted data from prying eyes. Within a week of performing the cryptography program, all content will indeed be translated to living thing-unreadable coding on your required drive.
If your mobile phone is damaged or destroyed — or if it is hacked or compromised by an intruder — you can absolutely guarantee that your system is protected. The attacker likely won’t check the information even without the respective key. When a computer is damaged or destroyed, and the documents or database are not protected, the data can be easily stolen by a criminal, and that it is a safe idea to safeguard your confidential data, if not all, of your storage device.
To obtain the information, the thief doesn’t have to remember the mark-on password – booting a device from a USB memory stick and afterward accessing the disks inside the machine is easy. Encrypted communication is a hard concept to understand, but it is an essential method of keeping confidential data about your companies.
Step by step guidelines on how to do disk encryption software
1. Authentication

An entire cryptographic scheme is just as effective as the authorization mechanism that enables users to unlock their devices, so make sure every invention you recommend provides a variety of two-component verification mechanisms such as using a card-based encryptor or even a USB key. Several other goods also make the use of biometric authentication as a critical requirement. Use either a program that can be connected to the company’s organizational authentication mechanism and destination address, including such Active Directory, might be the most useful for effective data management.
2. Key Management Recovery
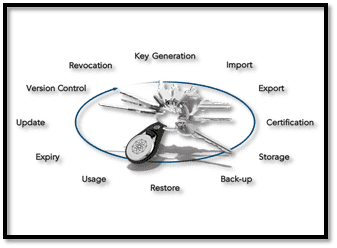
Perhaps one of the most significant concerns with filled to the brim multifactor authentication is that people can get knocked out of individual machines and not be able to function even though they have misplaced their credentials or misplaced their keys for second different passwords. Laptop computers and the data stored inside could also become unavailable if a female employee leaves the country, and there is no transfer of information.
That ensures it’s necessary to ensure that every FDE implementation you recommend has an acceptable multifactor authentication and restoration system that addresses your organization’s information security guidelines.
For fairly obvious reasons, several other management techniques provide self-service button retrieval-allowing users to easily navigate back through their applications after conveying data such as their name and date of birth or national insurance number. But if this does not include adequate protection for any or all users, you can look for a program that only mainly provides recovering through an operations manager.
3. Centralized Management and Deployment
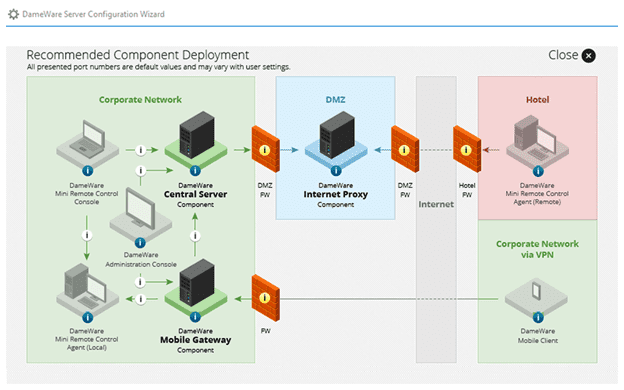
Several other full symmetric encryption operating system-notably that very many components for entirely free and open-source encryption-is constructed for personal usages and, therefore, must be implemented and optimized on the device. However, in evaluation and analysis, visiting every computer is not realistic for installing entire encryption technology.
FDE technology should be geographically programmed to maintain consistency and make it much easier to submit any improvements in the specification to any machine when appropriate. It is also strongly advisable for administrators to be able to squeeze down a massive password management installation process, so associated applications can’t change it. Searching for a processing system that integrates the framework could also be advantageous.
Searching for an organizational approach that incorporates or is part of a comprehensive framework that really can maintain all critical elements of threat intelligence, such as anti-malware software, and maybe even some windows server cryptography, might also be advantageous. It is therefore strongly advisable for administrators towards being able to squeeze away quickly the specification of a complete disk encryption method so that potential customers can not change it.
Those specific primary roles to search for in a management platform are distant location has taken measures and redesigning, and the willingness to modify the encryption algorithm that underlies it.
Last things you need to remember regarding disk encryption software
- You will need to use encrypted communication computers to determine authentication and encryption, which is responsible for encryption and decryption of all information on a particular road going.
- If having great software is running Microsoft windows specialist, implemented BitLocker, which seems to be the full password management operating system for Microsoft, could perhaps come along.
- It is necessary to have an excellent understanding of how encrypted communications performs because once making crucial decisions concerning cryptography.
- Encrypted communication is a digital method of authentication that uses complex equations to decipher transmissions, allowing the interface to be decoded only by entities who have the recipient’s code or password.
Conclusion:
The encryption algorithm is used to send a protected exchange of information between two people and organizations, as well as any other relevant information. All applications have both a username and a password key on communications sites, along with most other email accounts. The encrypted message functions as the measures a company’s ability and approach by which the intended recipient can send and receive their message. The communication is additionally encrypted with the permanent key to encrypt a message. The recipient will then use the public key from the recipient to actually verify the email and then access this information with its encryption key. A hacking group that transmits the statement will not be able to display its components without a unique number from the receiving antenna.