The data that one creates and uploads for business or personal use becomes a target for online criminals. Each click, each browsing, and each internet exploration one may make or break somebody’s life and career. That is why whenever you do, a certain form of caution has to be performed.
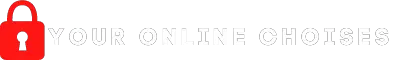
One of the most effective ways to protect your data is by installing so-called encryption tools or software. These are software made to transform the public data you input in the net into an encoded version of it or files that are locked. It can only be opened through the key or password set by the authorized person. It also uses an algorithm together with that key you set.
For the best choice to use, refer to the list below for the top 5 of all that file encryption you’ve desired from the internet.
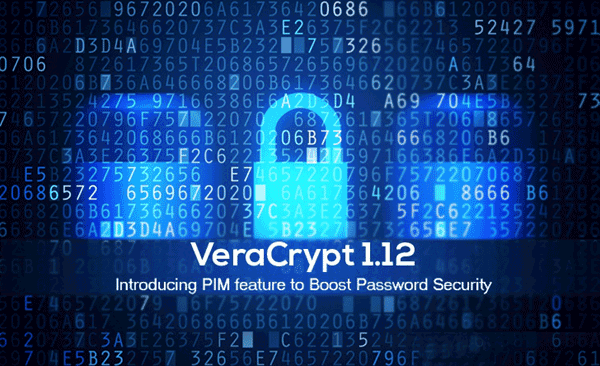
- VeraCrypt – this was from the lineage of TrueCrypt, which was just as good as this. It adapts to all kinds of OS and can support AES, Serpent, and Two Fish encryption codes. There is a lot of great things to talk about from this file encryption software. One is that it has a regular, up-to-date encryption program as it is always under development to easily adapt to what your file needs. However, the source that is very important in keeping files and data is not available at the same time. The workspace it has is not very user-friendly. VeraCrypt also does not have any other safety features. It works best for Windows, OS X, and Linux operating systems.
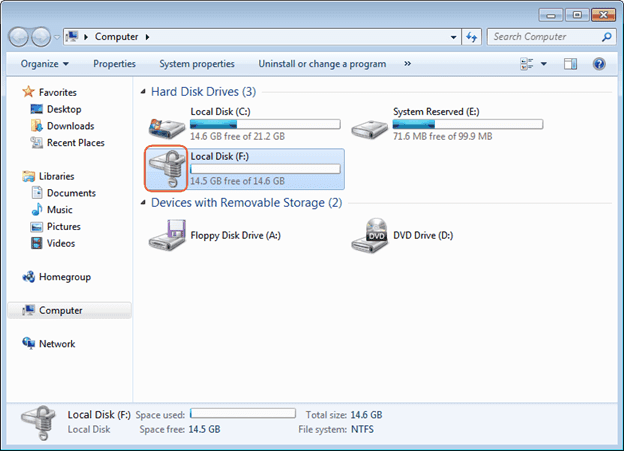
2. BitLocker – offers complete, holistic drive protection and encryption that can be expected for any Windows versions as a built in software. It creates a drive online that is easy to open. Also, this encryption software supports AES codes together with other authentication mechanisms. It is a trusted software for having a clear and easy technology on decrypting and encrypting files. On the contrary, it may put your work into compromise because of its non-functional protection to be used for business documents. Its downside, though, is that government agencies from different countries are given the privilege to open such files. Its creator, however, said that the accusation was not true that they do not really have such a feature.
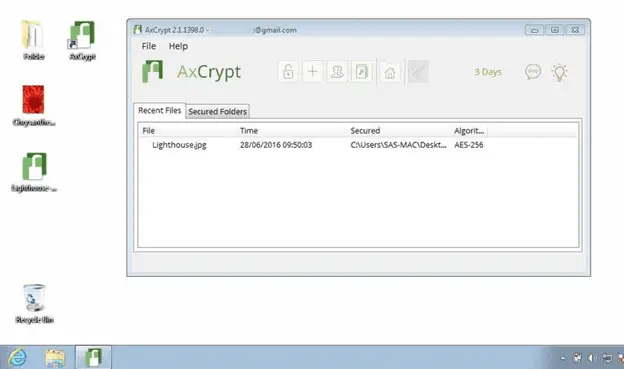
3. AxCrypt – a free, downloadable online source of file encryption tool that’s easy to be used by even beginners. In fact, you can decrypt files that it protects by demand or while you are using the file. Once you close the file again, the encryption automatically comes back again. It covers only a small amount of memory in your computer and delivers fast results, too. AxCrypt, however, is not recommended for business use because it cannot make documents for business, nor can it make drives secured. It’s easy and free but not that reliable. It can be vulnerable to some very serious threats online, which includes those that you may be stored in your iCloud accounts.
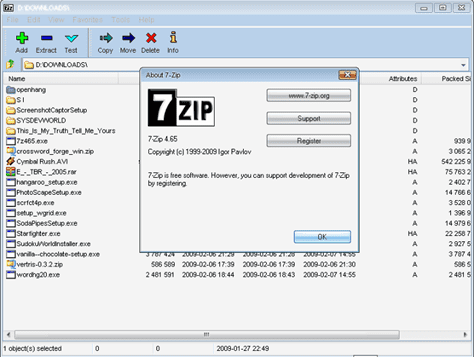
4. 7-zip – another free to download software for encryption that consumes only a small part of your computer’s memory while taking on a large number of files for encryption. The files are set to self-decrypt when used by its legitimate user. This encryption software is also allowed for 256 bit ASL encryption software. But, it cannot be used for making documents that are secure for business use. At the same time, this encryption software is not a reliable one in terms of speed and strength in its protection of your files. In a click away, this encryption can be decrypted as it easily becomes one with your OS shell, such as Windows.
5. GNU Privacy Guard – ready to serve users of Windows, Linux, and OS X is this encryption software that can be easily found free to install online. This is the type that can encrypt even your emails and larger files like your entire drive and other media files. Business documents, however, cannot be securely created. Each file has to be encrypted, too, one by one by its user.
Advantages of Using Encryption Tools
Aside from its assisting powers in terms of safeguarding your data through a lock key, this tool is also advantageous because some organizations and companies require the sensitive information they share with their employees to be safely locked away from scammers and hackers’ hands.
It also prevents third party players in the scene, especially when it comes to financial or money matters. Thus, strictly securing the data avoids losing money unknowingly.
Disadvantages of Using Encryption Tools
Legitimate, authorized users may also not be able to open a certain set of data and digital information because of its high-grade security that is hard to cipher.
It shall take a while before it can retrieve all important information if anything happens to malfunction. For instance, if a virus infects your computer and you are left with the choice of just to delete all of your data, it would be hard because of the long process.
Lastly, the government’s privilege of prying open into your personal files when the need arises may be considered a disadvantage, too. One’s privacy needs to be 100% ensured and guaranteed.
Tips for Stronger, More Improved Security
Because encryption is never enough, matching it with the right caution is still advised. There is a need to impose more than one stage of security, so your files, especially if you are a blogger, can be safely secured.
- Always check for updates on your browser, operating system, as well as your antivirus software to ensure up-to-date protection as well. Those are free to download and just as safe, too.
- Never or at least be careful when using open Wi-Fi connection jus anywhere you like. This makes your device even more prone to online viruses and other intruding elements.
- Study and read about how to further enhance your knowledge of securing your own data and identity.
Final Thoughts
Having these encryption tools can be much of a relief to any user. Many things today revolve around technology and that most of the people’s life is affected by it. Those data you share may be just words, but the impact it will have on your life and those of other people around will be great. It shall be a forever goal, for as long as you keep on using the Internet all different forms of technology, to protect yourself and your data from privacy intruders.