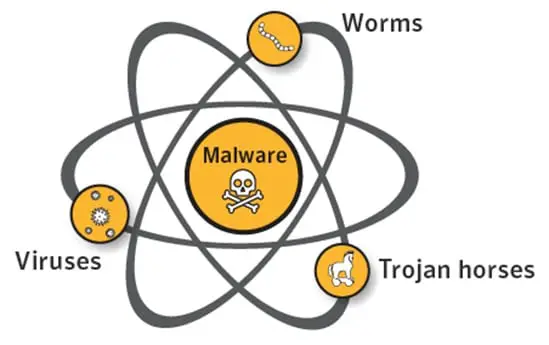
Malware is a shortcut for ‘malicious software.’ It’s a blanket word for worms, trojans, viruses, and other maligned computer programs used by hackers to obtain sensitive information. So they can cause a mess online.
It also refers to software that is formed to impair computer networks, servers, and computers. It’s not about the technology nor a particular technique that is applied to it, but the concern is the intention of its usage.
A virus is not the only type of malware. Yes, all kinds of viruses are malware like biology is to science. It’s security terminology, and you can learn more by getting familiar with other types of malware. To know how to check for malware, please continue reading.
How to Check for Malware: Different Types
1. Virus
Most of the regular users of the new technology call all types of malware ‘virus’. You should know that not all malware programs are viruses, and you should be thankful for it. It’s the sole type of malware that infects files.
The virus that would dwell in your computer can modify your legitimate files. In this case, you can only execute the virus if you delete the files that it coheres with. So, it plainly shows that it’s difficult to get rid of them. The best anti-virus would struggle to correct the legitimate file and would eventually quarantine or delete it in most cases.
It’s a good thing that it became uncommon nowadays. It comprises less than 10% of all the malware.
2. Worms
Worms came earlier than viruses. The email surfaced around the late 1990s together with them as worms were attached to the mails. Computer security professionals see this as a challenging undertaking. When worms are in just a single mail, it will infect the whole company in no time.
It has a nasty trait to ‘self-replicate.’ Take the iloveyou worm as an example. It swept almost the entire world as it took down TV networks, delayed newspapers for half a day, and overloaded phone systems. Other worms called MS Blaster and SQL Slammer have their place in the history of computer security.
It has this awesome ability to move by itself without needing action from the user. On the other hand, viruses need to be clicked by the user before it can infect files. Worms can manipulate programs to do some harmful jobs.
3. Trojans
Trojan horse replaced worms as the weapon for hackers in attacking devices. It acts as a legitimate program, but it bears malicious instructions. It’s been existing like forever compared to the presence of viruses.
Trojan must be allowed by the user to conduct its intention. It is usually on infected websites and goes along with emails. The most common disguise of Trojans is by acting as an antivirus program. It would notify the user that the computer is infected and would ask for permission to clean up. Once the user lets it proceed, it does its dirty job.
It’s not easy to defend your devices from Trojans. A firewall or another sort of defense can stop. It’s being released by millions each month while anti-malware software tries their best to eradicate them, but there’s a need for a lot of signatures to do so.
4. Exotic and Hybrid Forms
A combination of Trojans and viruses or worms come out these days. For instance, Trojans are allowed, but it attacks the network in a way a virus would do. This form of malware is considered a stealth program and rootkit.
It tries to alter the present operating system so it can take control so it can’t be detected by the anti-malware program. It can be eliminated by deleting memory component control done in an anti-malware scan.
5. Ransomware
It can cripple hospitals, police departments, companies, and even the entire city. It has the function of encrypting data, which makes a hostage for cryptocurrency to grow a huge percentage of malware.
Most ransomware programs take up the form of Trojans, and they apply for the wait-and-see advances. They establish the encryption routine by watching the user for hours. The malware’s admin can figure out the amount of ransom the user can afford. Safe back-ups can also be encrypted or deleted.
Prevention can be applied, but it’s hard to reverse the damage if you don’t have a good back up with validation. A study came up with the result that 30% of the victims weren’t able to retrieve their files even if they paid the ransom. Just to be sure, you need to have an offline backup for your files.
6. Fileless
This section shows more on how malware can persevere and exploit rather than the type. Traditional malware maneuvers and infects a system by files which are actually fileless. It occupies 50% of malware these days, and it continues to grow.
It usually clings with non-file objects like APIs, scheduled tasks, or registry keys. It exploits legitimate programs by making it a sub-process. It sometimes uses built-in tools found in Microsoft’s PowerShell. So it results in the difficulty of finding and detecting it.
7. Adware
You’re lucky if you only met a malware called adware. Its job is to endanger the end-user to undesirable, malicious advertising. You can be redirected to searches with look-alike web pages that are filled with product promotions.
8. Malvertising
It creeps through ads or ad networks that are legitimate. A cybercriminal places an ad on a legitimate page. When the unsuspecting user clicked it, he or she was directed to a prompt that would install the malware on their computer or a malicious website. In some cases, the ad automatically comes on by the process called ‘drive-by download.’
It usually attacks legitimate networks that carry many ads such as the New York Times, London Stock Exchange, and Spotify. The users of these sites are at risk of malware. Cybercriminals have goals to get money from them.
9. Spyware
Spyware is sometimes used by persons to monitor their loved ones’ activities when suspicions arise. Criminals find it useful to attack someone online. They would use it to obtain passwords and intellectual property.
Like adware, removing it is no sweat. Its intentions are not as wicked as other types of malware. You can execute and prevent it from bothering you.
The thing you have to worry about is the used mechanism, which can be social engineering, unpatched software, exploitation of the user or the computer, and other dozens of exploitation cases. It breaks in like the Trojans’ style. When you see a sign of it, you have to correct it.
How to Check a Malware: Detection and Prevention

Detection of Malware
Despite your carefulness and effort, the malware was able to get through obstacles and infect your devices. Knowing this would need you to level up to corporate IT. You will come to know that there is an advanced visibility tool that would let you see the happenings in your network. It is great at detecting infections done by malware.
There’s a wide range of detecting network tools. It can cost from one to a few thousand US dollars. SIEM tools are one of them, and it is also associated with log management. It is capable of tracking down previous logs throughout your infrastructure. It would check your computers and appliances for malware attacks.
Essential Steps to Know if Your Computer is Infected by Malware
1. Your computer should be connected to the internet. Open the Microsoft site Systinternals.com.
2. Download Process Explorer. You don’t need to spend anything on it.
3. You have to unzip and use procexp.exe.
4. Do the right click so you can run the program, so it works as an Administrator for the security context.
5. Run the program and go to the menu. Choose and check VirusTotals.com. All of the running executables will be submitted to this website, which is managed and maintained by Google.
6. Click ‘yes’ to accept the license. Close it, and you can go back to Process Explorer or Autorun.
7. You will see a column entitled Virus Total. It will give you a ratio like 0/67, 2/67, or 19/66. The antivirus engine equates to 67, but it goes up and down all the time. You will see the first or the digit above the antivirus engine is the number of malware. You’ll be glad if you have it in zero. If you see 57 for the antivirus engine, it is an indication of false positive.
Getting Rid of Malware
It can be a tricky procedure. The exact method will be based on the type of malware that brought the infection. The providers of visibility and detecting network tools can give you the needed procedure. They would show you how to edit the Window registry so you can endure the predicament and move on.
Protection Against Malware
The antivirus software is the most well-known as the most popular malware is called a virus. You may hear that high-end security pros brush off this idea. But it can’t be denied that it is the backbone of the defense against malware, although it’s the basic. You can search for the best anti-malware software.
The advanced corporate ones offer endpoint security. They don’t only provide the signature-based detection of malware. They have more services such as personal firewall, application control, anti-spyware, and more prevention styles against intrusion.
Final Applause for Knowing How to Check for Malware
You know now that there are different types of malware and the nature of their attack. So you will be able to distinguish them and prepare how to avoid and block them. You have to get a detecting network tool to help you. It will make you safe online, and it can do the necessary job for you when mishaps occur because of malware.