Malware nowadays is becoming more rampant than before as technology evolves every day, too. Not one device is no longer completely safe from such destructive elements, not even Mac. Yes, that’s true. Mac is now permeable by malicious software content wherein. Usually, users are not aware of because they are just too good at disguising.
One of the most notorious of them all is the Cryptolocker that can be very brutal at invading your computer and your files. So, you’re now worried about your devices being corrupted and would like to ask, what type of malware is Cryptolocker? Find out the answer below.
What is Cryptolocker?
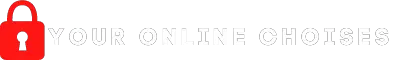
Malware level up each time and CryptoLocker is not an exemption to that. Instead of just creating duplicate files from your computer, eating up your memory, and sending you Ads and some pop-up messages, this malware makes a way to lock all your important files to encrypt it.
To open an encrypted file by CryptoLocker, users have to pay a certain amount of fee first. Like being kidnapped and abducted, malware like this one has been known as “ransomware” by experts and the victims of this virus.
CryptoLocker uses various ways to successfully hack someone’s files and computers. It can be in your email, social media, and usually, in downloads. This often happens with users completely unaware for it is not easy to tell which ones are fake files or websites, and which ones are real. But, with the help of most powerful anti-viruses today, this should no longer be a problem because it is super easy to do. The first thing to do is learn more about how to tell if your computer is infected by continuing, which you may do so by continuing to read.
How to Know When Computer is infected
If you are using your computer regularly, then it should be easy for you to observe anything abnormal and unusual happening to your computer. At the same time, as a loving owner of a PC or device, it might have been in your mind to install an anti-virus as soon as you began browsing the internet and all other online activities that you are used to doing.
- Your computer suddenly becomes too slow and unresponsive in operating some files. This can be just a normal scenario, especially if your storage is already running low. However, if you checked and knew that it is not the case, then that can be a sign of infection.
- Various pop-ups and Ads show up in your computer that never or rarely happened on your PC. Those pop-ups are from some internet malware nowadays that are too obvious and which is fixed immediately using an anti-virus.
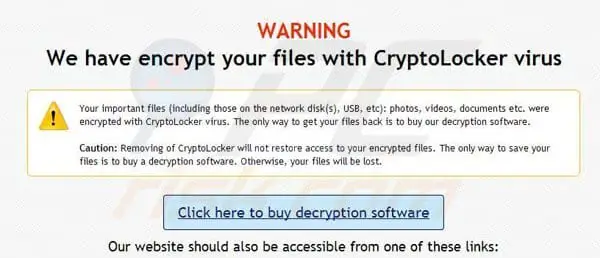
That’s all for your observation to support whatever examination your chosen virus removal app will have afterward. Once you run an anti-virus on your device, that is the only time you can confirm your suspicions. To run an anti-virus, you have to:
- First, you must have backup storage for your files that are important to you and that you trust not to have been infected yet. Make it a habit to always scan before restoring files from your backup storage.
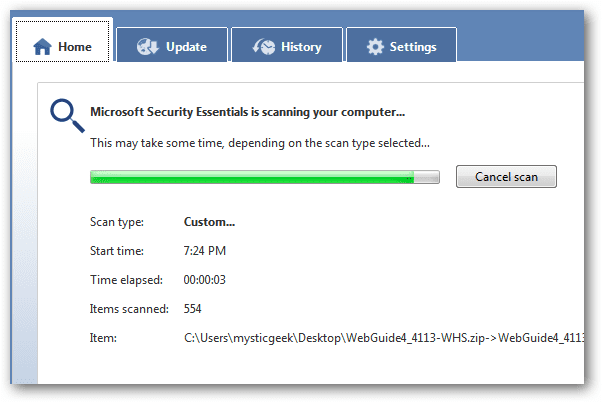
- Download your desired anti-virus online, even those that have a free trial. In those days free of charge, you must have been already finished backing up your files, too. Observe if the anti-virus is really what it is meant to be. Thus, before accepting its download completely, it is important also that you scan its content and details closely, first.
- You might have to disconnect from the internet for a while so that no malware can cross or hack your system. To succeed, hackers need to communicate with other computer servers and others they are working with.
- After everything has been prepared and nothing else has been left in compromise, you can now install your desired anti-virus as well as the necessary updates to be downloaded. Start a complete virus scan, including those that you will be restoring.
- Make it a habit to always scan your files for any possible infection, especially when you had just downloaded, installed, or visited any unfamiliar file to your computer.
Once you have successfully cleaned your files and computer of all possible viruses and you wanted to keep it as clean as that all the time, then knowing how to prevent such a scenario from happening again maybe your next goal.
How to Prevent it
Accidental or not, it is every PC owner’s responsibility to keep their devices safe and secure all the time, which is also for their benefit. Without viruses, they can be sure that the files they upload are kept confidential, too.
So, here’s how to prevent viruses and malware from bothering your computer ever again.
– Install a good antivirus or maybe a malware software to be sure.
– Always update
– Have a regular schedule for the scanning of files using a trusted antivirus
– Make strong password protection on your network, such as your Wi-Fi connection.
– Observe closely each time you click a specific website. Never click any website that offers some suspicious, disguised information.
– Don’t connect to the public or some open internet connection where many people are connected, too.
– Always keep a backup of your precious files.
– Always secure your personal information and never share them with just anybody.
– Change your password more often. Use passwords that are strong and hard to be guessed by hackers.
Other Types of Malware
Aside from CryptoLocker, other malware already exists nowadays, which are also uniquely destructive in their respective ways. Those are:
- Locky – ransomware since its release in 2016. It can encrypt and hack 160 files after the user has been tricked into installing the file after clicking some fake and infected files from emails. Also, it is well-known for this phishing activity. Mostly, it targets computers owned by engineers, testers, and designers.
- WannaCry – pervaded in a maximum of 150 countries in 2017. At the same time, its rumored creators were the United States National Security Agency, later on, released secretly by the Shadow Brokers group. Its aim was to make vulnerable exploits in Windows. Over 230,000 PCs have been infected by this malware back then.
- Bad Rabbit – Launched in 2017, this ransomware has attacked various computers through its ‘drive-by’ method. It means that using this ransomware, and another malware gets to be launched to infect users who click carelessly on legitimate websites.
- Ryuk – this ransomware is made to disable and encrypt several types of network drives, systems such as Windows System Restore option, and others. It started to exist in 2018.
- Troldesh – begun to damage computers in 2015 and has spread through emails and attachments since then. Unbelievably, the hackers made direct emails to victims, actually asking and negotiating for discounts on ransom.
- Jigsaw – Been named after the famous Saw film and started its attack in 2016. Because of its connection to the said horror film, extra distress is felt by victims, aside from its normal attack of gradually deleting files of users. This shall continue until the ransom has been paid or everything’s gone.
- Petya – the former name of GoldenEye, which was born in 2016 and resurfaced in 2017. Instead of the common attack made through encrypting certain files, this ransomware works on your whole drive using its MFT or Master File Table to lock the disk from being accessed.
Final Thoughts
Technology truly have brought innovative ways to live life. However, along with that are these dangerous viruses born from the cunning use of the internet. Change is inevitable as malwares continue to grow in number each day, too. Keep this information in mind so you’ll know how to deal with these problems on your own in the future.